Library workers at Western University’s Graduate Resource Centre in London, Ontario, had a workshop from Alison Macrina, the library organiser whose Library Freedom Project won a battle with the US DHS over a library in New Hampshire that was offering a Tor exit node as part of a global network that delivers privacy, censorship resistance, and anonymity to all comers. Western’s librarians were so taken by Macrina’s presentation that they’ve turned on Canada’s first library-based Tor node. There is no clear law in Canada about libraries and Tor, and Macrina and the Western library folks say they’re spoiling for a fight. READ: First-ever Tor node in a Canadian library | Boing Boing
Tag Archives: cybersecurity
CyberWar Threat [YouTube Video] | NOVA #tech #hacking #cybersecurity #documentaries #telecommunications #Internet
The global cyberwar is heating up and the stakes are no longer limited to the virtual world of computers. Now, thanks in part to secret documents released by Edward Snowden, the true scale of the National Security Agency’s scope and power is coming to light. Besides spending billions of dollars to ingest and analyze the worlds’ electronic communications, the NSA has set out to dominate a new battlefield—cyberspace.
NOVA examines the science and technology behind cyber warfare and asks if we are already in the midst of a deadly new arms race. Already, highly sophisticated, stealthy computer programs such as the notorious Stuxnet worm can take over and even destroy the control systems that regulate everything from food factories to gas pipelines, power plants, and chemical facilities—even our cars. While the destruction of Iranian centrifuges may have delayed Iran’s bomb program and forestalled an Israeli attack, the attack has opened a Pandora’s Box, and now America’s own critical infrastructure is vulnerable to retaliation and attack. With leading defense experts and investigative journalists who have probed the murky realm of criminal and strategic hacking, NOVA examines the chilling new reality of cyberwar in which no nation or individual is safe from attack.
SOURCE: Cyberwar Threat | Full Documentary HD |Our World in HD | NOVA | YouTube
#Emoji #Passwords are Coming: Harder to Hack and Easier to Remember | Gizmodo #cybersecurity
I wonder what we do if we don’t remember which Emoji character we used for our “Emoji Code”…there are too many Emoji now IMO…and with so many accounts as a techie I’m sure won’t remember them all if Emojis are eventually used for logins of services beyond just bank accounts.
A UK company claims to have invented the idea of using a set of emoji to replace a PIN number, suggesting that our stupid brains find it easier to remember the silly drawing people face things — and that the increased complexity of the emoji character set makes brute-forcing into our bank accounts substantially harder. READ MORE: Emoji Passwords are Coming: Harder to Hack and Easier to Remember | Gizmodo.
Career Spotlight: What I Do as an “Ethical Hacker” | LifeHacker #cybersecurity #hackers #hacking
You occasionally hear about major security vulnerabilities being discovered before they’re exploited, like the notorious Heartbleed bug last year. Security researchers work hard to weed out those dangerous flaws before they’re found by hackers of more malicious intent. This breed of preemptive hacking is sometimes referred to as white hat, or simply “ethical hacking.”
These hackers work with businesses to probe their networks for security holes, vulnerabilities to social engineering, and more, while considering the mindset of someone who might have criminal motivations. To learn about what such work is like we spoke with Ben Miller, an ethical hacker at Parameter Security. READ MORE: Career Spotlight: What I Do as an “Ethical Hacker” | LifeHacker
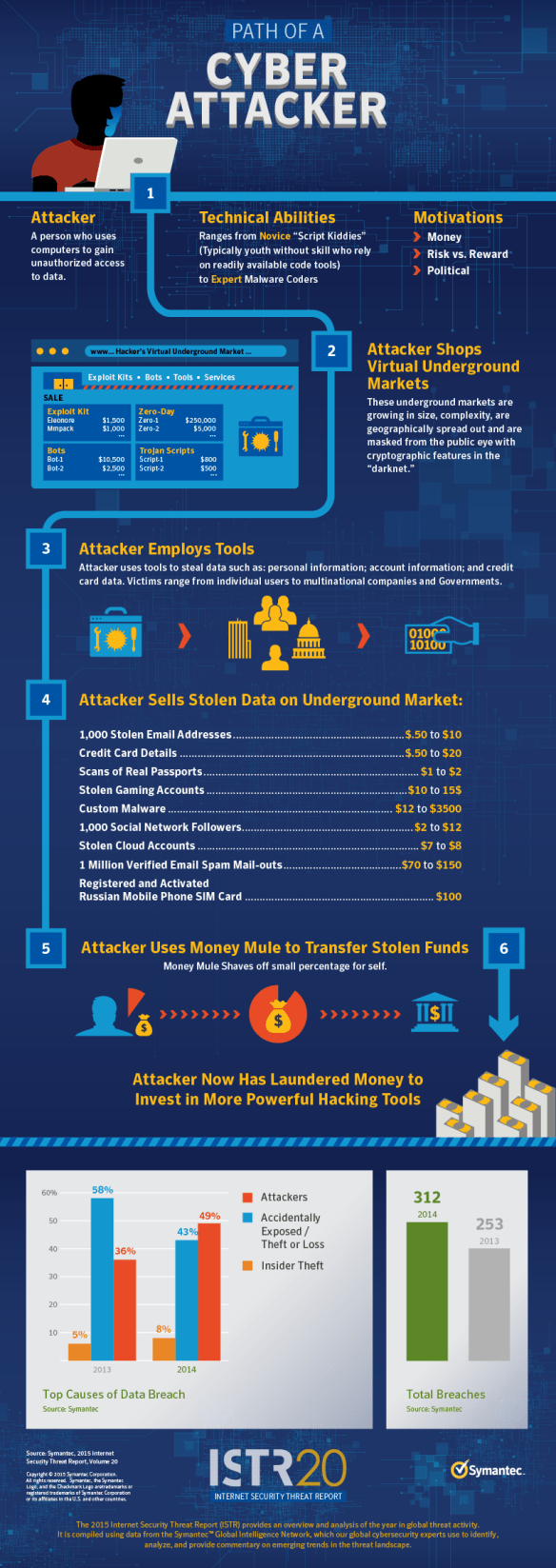
Symantec’s 2015 Internet Security Threat Report, Volume 20 | Symantec.com #cybersecurity
2015 Internet Security Threat Report, Volume 20 | Symantec
The Internet Security Threat Report provides an overview and analysis of the year in global threat activity. The report is based on data from the Symantec Global Intelligence Network, which Symantec’s analysts use to identify, analyze, and provide commentary on emerging trends in the dynamic threat landscape.
▶ Symantec’s 2015 Internet Security Threat Report: The Cyber Landscape | YouTube.
9 Facts About Computer Security That Experts Wish You Knew | Gizmodo
Every day, you hear about security flaws, viruses, and evil hacker gangs that could leave you destitute — or, worse, bring your country to its knees. But what’s the truth about these digital dangers? We asked computer security experts to separate the myths from the facts. Here’s what they said.
READ MORE: 9 Facts About Computer Security That Experts Wish You Knew | Gizmodo
Cybersecurity Lab | NOVA Labs | PBS
The Cybersecurity Lab is a game designed to teach people how to keep their digital lives safe, spot cyber scams, learn the basics of coding, and defend against cyber attacks. Players assume the role of the chief technology officer of a start-up social network company that is the target of increasingly sophisticated cyber attacks. In the game, players must complete challenges to strengthen their cyber defenses and thwart their attackers. The Lab also features stories of real-world cyber attacks, a glossary of cyber terms, and short animated videos that explain the need for cybersecurity, privacy versus security, cryptography (cyber codes), and what exactly hackers are. MORE: Cybersecurity | NOVA Labs | PBS.